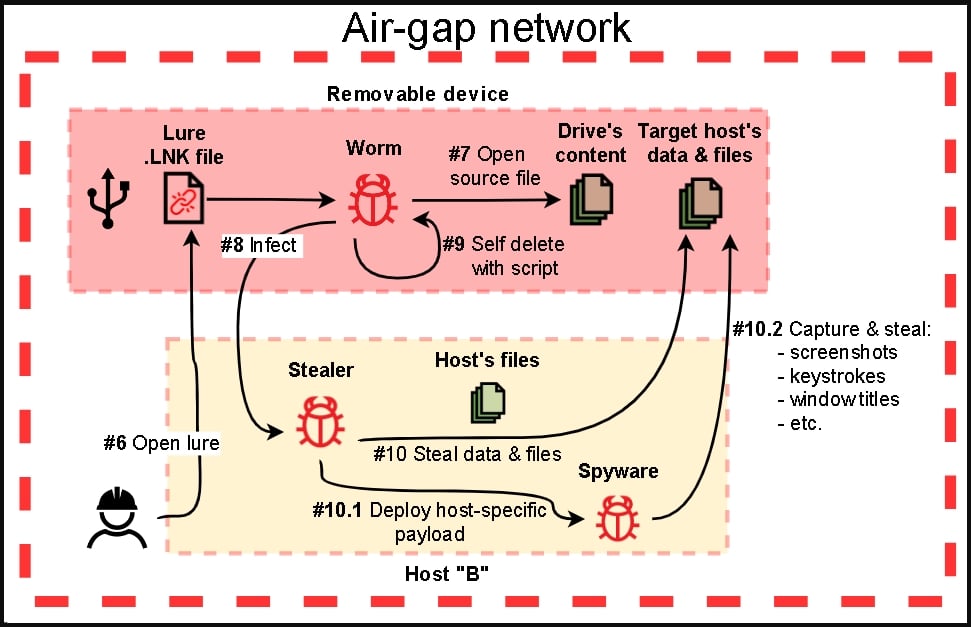
Hacking the Air Gap: Stealing Data from a Computer that isn't Connected to the Internet | Science Project

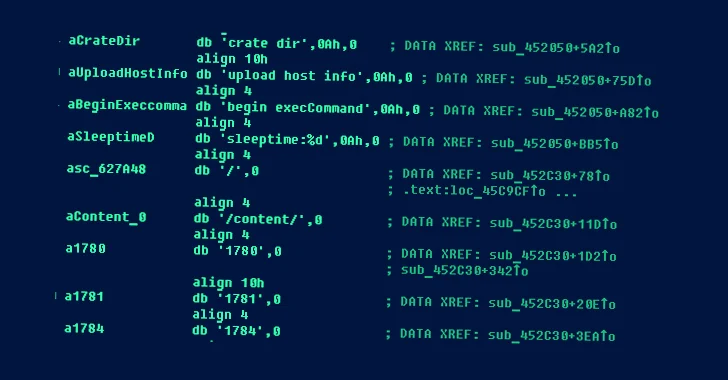
How Russian spooks hacked Microsoft, the gap in its “morally indefensible” response, and what CISOs can learn from the attack

Did #GAP's Instagram get hacked? It's now posting #YZY designs after deleting all of its previous photos and making the YZY brand logo its… | Instagram

security hack Threats of data leaks and system security Red open key surrounded by blue closed Close the problem solving gap. Ethical Hacking and Professional Penetration. Stock Photo | Adobe Stock



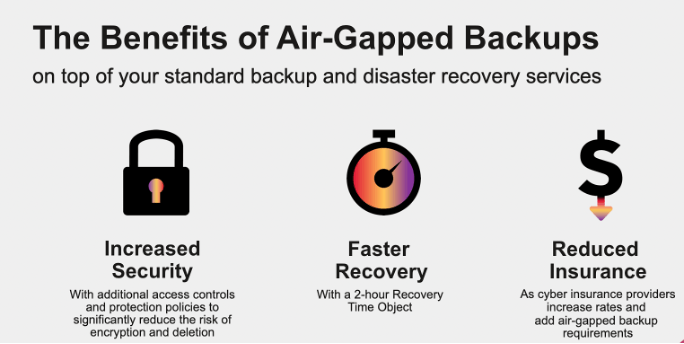









![Using an Air-gapped Computer or Network in 2024 [Price & More] Using an Air-gapped Computer or Network in 2024 [Price & More]](https://www.cloudwards.net/wp-content/uploads/2022/02/Using-an-Air-Gapped-Computer-The-Best-Defense-Against-Hacking.png)